E-TIE: External Threat Intelligence Engine
Security Starts With Intel.
E-TIE is the analytical environment behind RudieSec’s external cyber threat intelligence work. It is designed to support disciplined collection, structured processing, and intelligence development across a wide range of external sources, helping our analysts move from scattered signals to usable understanding. Rather than functioning as a “black box,” E-TIE is built as a layered ecosystem that supports how experienced operators actually work: gathering information, organizing it, evaluating relevance, identifying patterns, and developing intelligence that can inform proactive cybersecurity decisions.
Each layer of E-TIE plays a distinct and critical role in that process. External source collection feeds the system with relevant threat-facing information from outside the client environment. Information is then processed, structured, and fused in ways that help surface relationships, movement, and developing indicators across the broader threat landscape. Analytical support layers strengthen visibility into patterns, trends, and potential implications, allowing RudieSec’s analysts to produce clearer, more targeted intelligence for the organizations we support. Throughout the process, the analyst remains in control. E-TIE strengthens human judgment, it does not replace it.
Just as important, all of this work remains on the RudieSec side. E-TIE does not require client integrations, internal agents, API connections, or any technical access into a client’s systems or networks. Clients are not asked to implement a new platform, manage supporting infrastructure, or create operational dependencies in order to benefit from the intelligence process. That technical separation is deliberate. It allows RudieSec to operate externally, focused on the threat landscape outside the firewall, while clients receive the benefit of a dedicated intelligence capability without adding burden to their own internal environment.
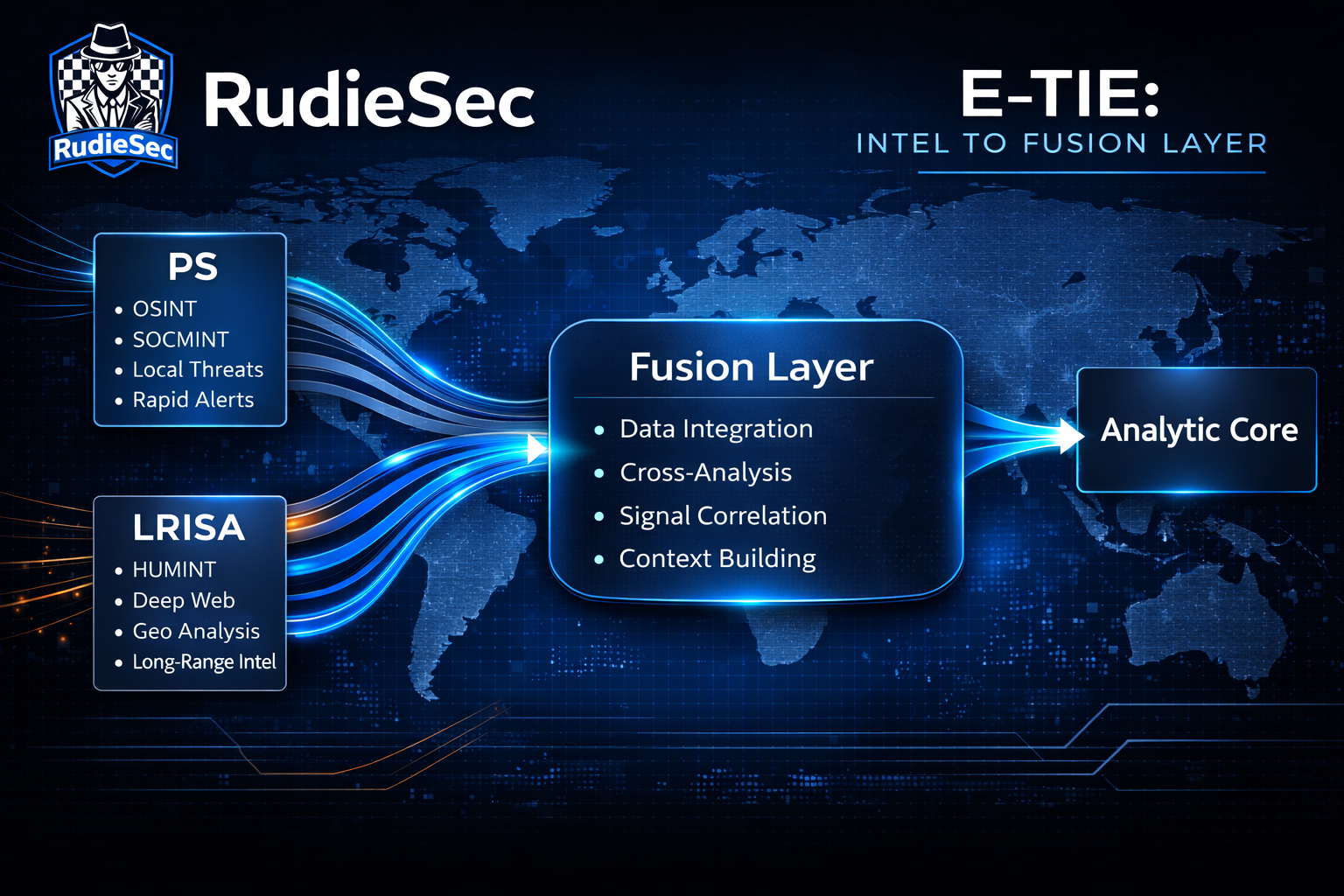
External Threat Collection to Intel Fusion Layer
Perimeter Scouting (PS) and Long Range Intelligence Support Activities (LRISA) operate as simultaneous external collection paths within the system intelligence process. They do not serve the same range or purpose, but they do work in parallel. Together, they collect externally derived intelligence across multiple streams, including OSINT, HUMINT, and SOCMINT. Given its longer-range focus, LRISA also extends collection into less visible and harder to monitor areas of the external threat environment. This gives RudieSec both a closer, client-bound view, and a wider view of the external threat landscape.
Perimeter Scouting focuses on the nearer threat horizon. Its collection is shaped by a client’s business operating sector, technology stack, exposed services, dependencies, and external attack surface. LRISA works across a broader environmental and temporal frame. It tracks shifts in adversary behaviors, infrastructure patterns, attack campaign movements, and other changes that may shape future risk. One path stays closer to the client’s immediate reality. The other looks farther outward and over a longer period of time.
The fusion layer brings these collection streams together. Signals from PS and LRISA are organized, contextualized, assessed, and combined into structured intelligence. This is where separate observations begin to form a clearer picture of present relevance and emerging risk. The result is not raw reporting. It is fused intelligence that supports analysis, forecasting, prioritization, and more informed client decision-making.
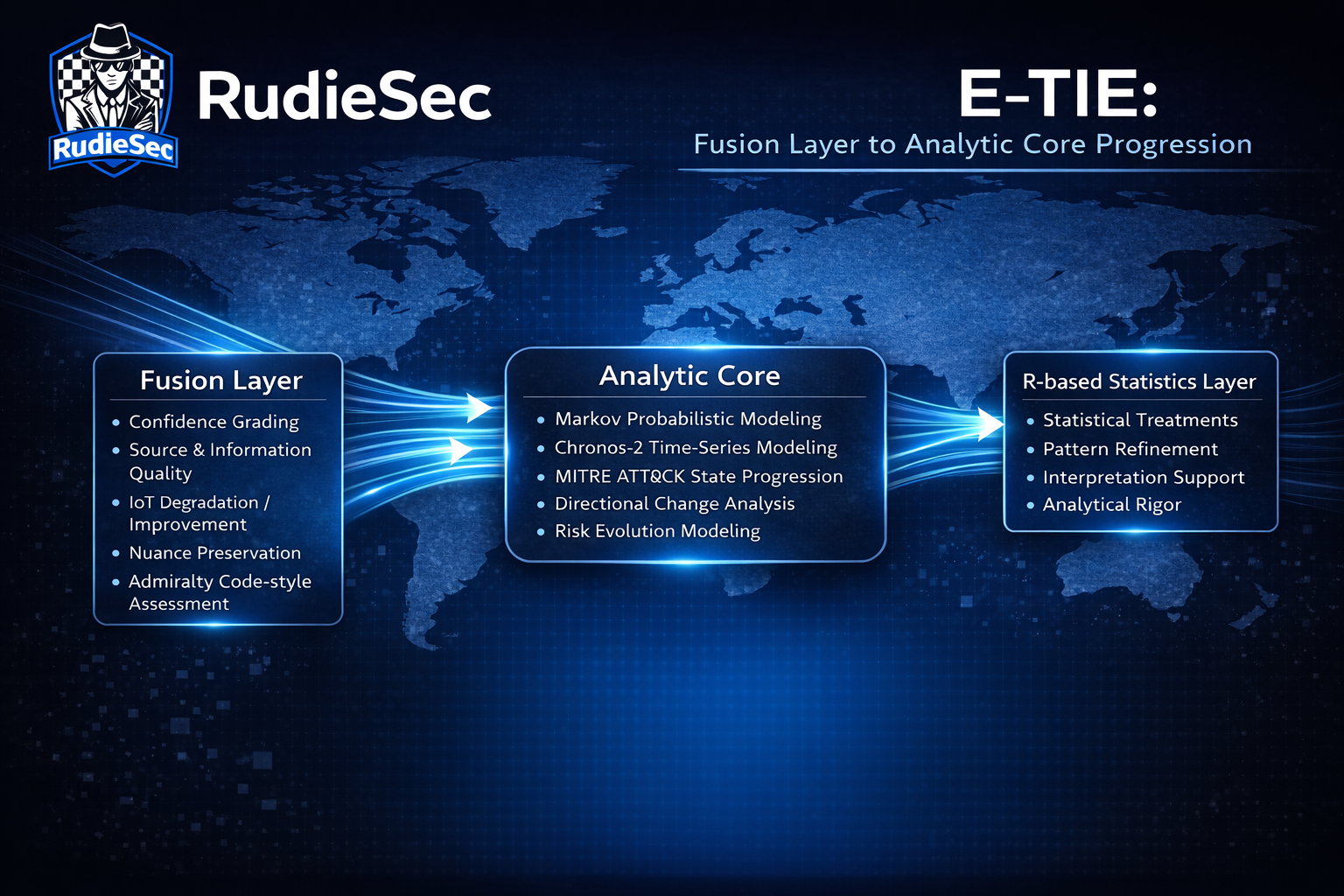
Fusion Layer to Analytic Core Progression
Within the Fusion Layer, intelligence is introduced to a series of structured evaluations before moving further in the system. Confidence can be graded, source and information quality can be weighed, indicators can be degraded or improved over time as relevance shifts, and nuance can be preserved rather than flattened into simple yes or no judgments. This layer is also where tradecraft-driven approaches such as Admiralty Code-style assessments help bring discipline to how signals are interpreted, prioritized, and retained. The result is a more refined intelligence picture, prepared for deeper analytic work inside the Analytic Core.
The Analytic Core takes the refined intelligence emerging from the Fusion Layer and advances it through E-TIE’s central modeling components. Markov-based probabilistic modeling and Chronos-2 time-series modeling are applied here to examine how threat activity behaves across time, conditions, and shifting patterns of relevance. MITRE ATT&CK defines the attack progression states used within the Markov model, anchoring quantitative/probabilistic analysis to a structured view of adversary behavior. This allows the system to model movement, estimate directional change, and develop a more structured understanding of how observed risk may evolve. From there, selected outputs move into the R-based Statistics Layer, where additional statistical treatments help sharpen interpretation and reinforce analytical rigor.
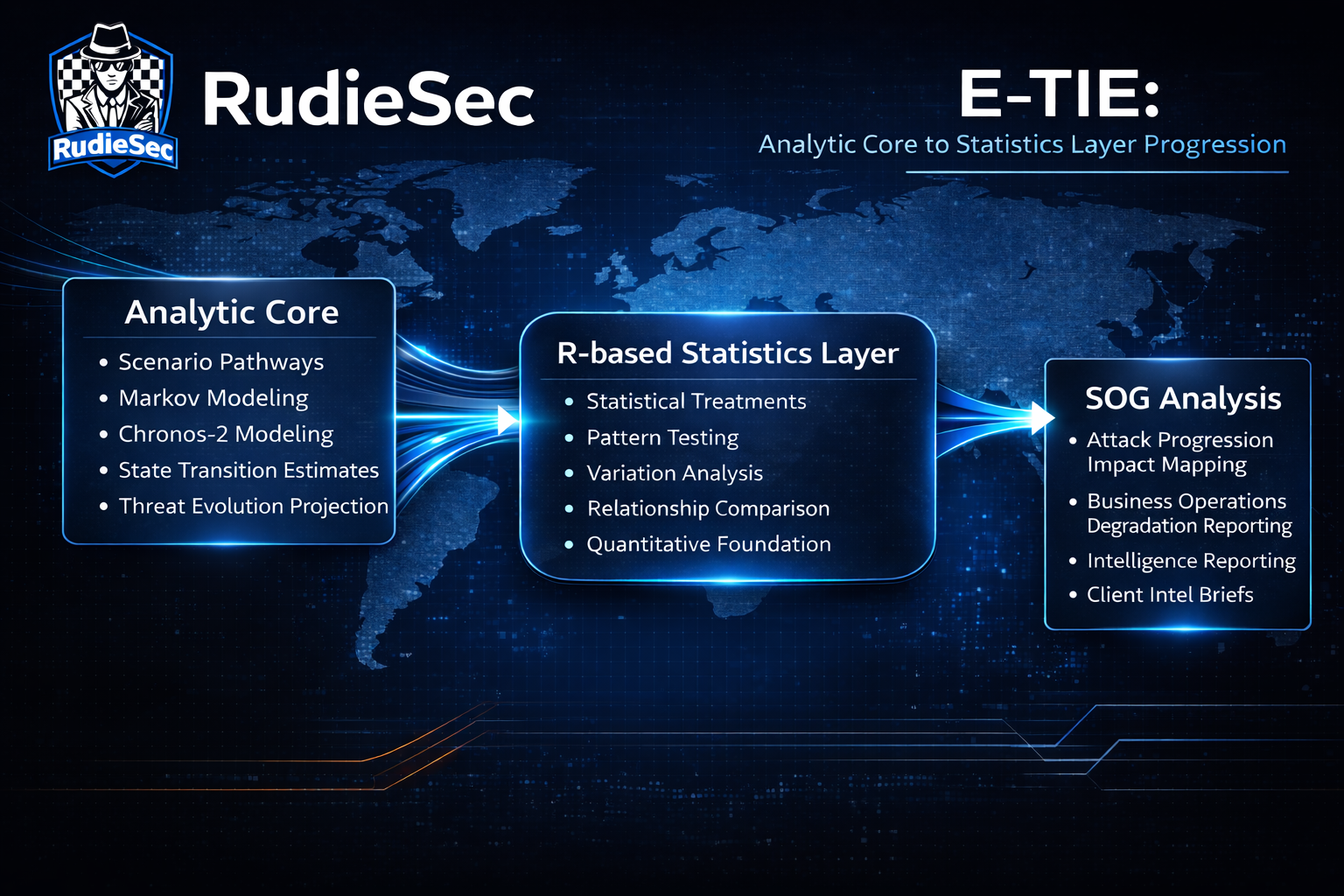
Analytic Core to Statistics Layer Progression
The Analytic Core progresses fused intelligence into scenario-based pathways. Markov and Chronos-2 do more than help describe what has already been observed. Together, they allow E-TIE to model possible directions of development, estimate how threat activity may transition from one state to another, and forecast how those transitions may unfold over time. This creates a more forward-leaning, proactive analytical deliverable, deliverable outputs that can be compared, stress-tested, and carried forward into the R-based Statistics layer for deeper quantitative examination.
The R-based Statistics Layer takes the scenario-based modeling of the Analytic Core outputs and applies additional statistical treatments to help make them more usable for downstream SOG Analysts. Here, patterns can be tested more closely, variation can be examined, relationships can be compared, and modeled outputs can be refined into forms that are easier to interpret with confidence. This layer helps transform computational outputs into analytically useful support, giving later-stage analysts a stronger quantitative foundation on which to assess movement, significance, and the weight of emerging threat developments.
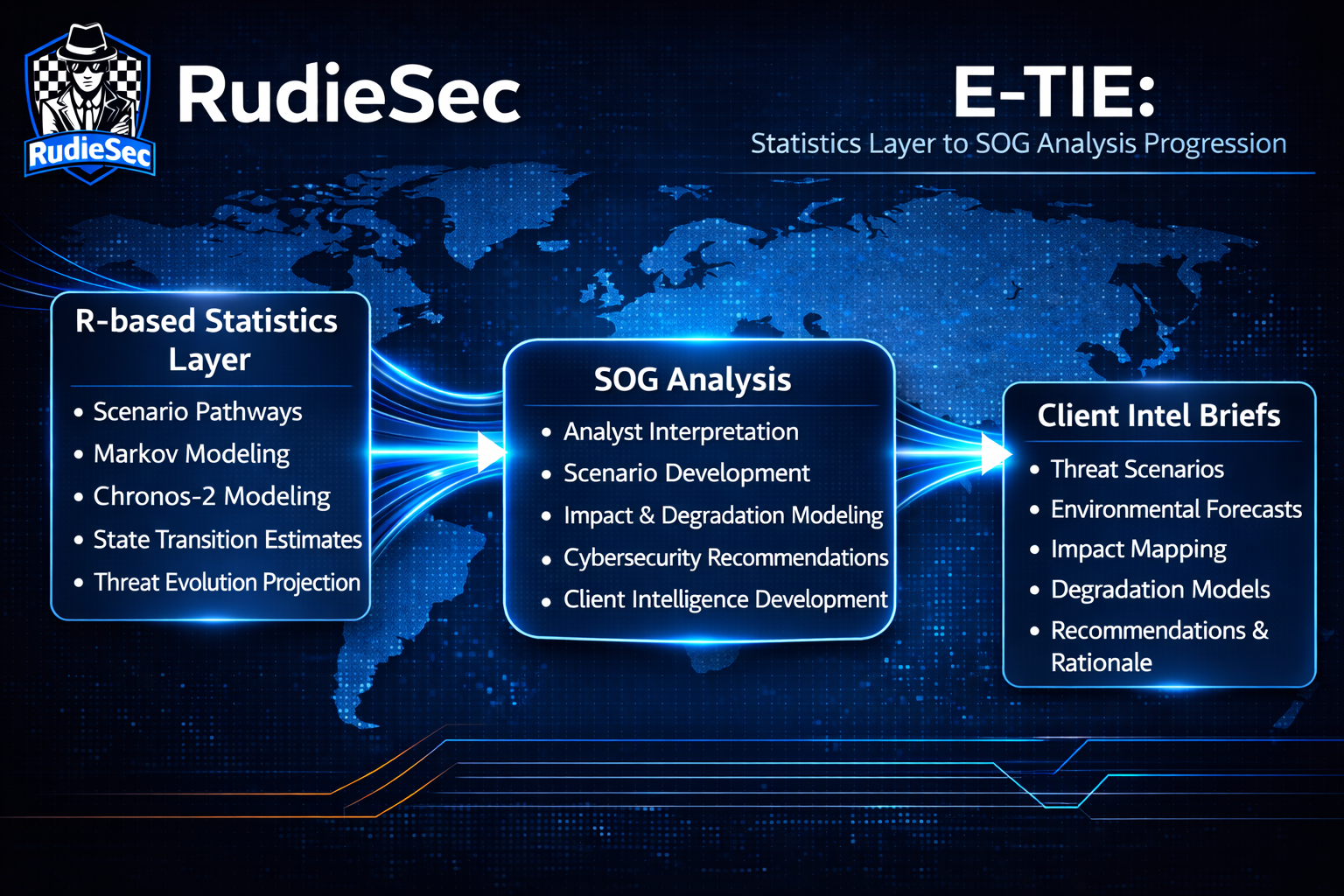
Statistics Layer to SOG Analysis Progression
The deeper value of the R-based Statistics Layer emerges as those treated outputs from the computational block begin moving toward human analysis. By the time the outputs move beyond the R-based layer, they have been statistically strengthened for deeper analyst use rather than left as raw computational results. This gives our SOG (Studies and Observations Group) Analysts a more disciplined quantitative basis for weighing emerging threat movement, comparing modeled developments and forecasts, and determining which patterns carry the greatest practical significance for a client’s environment. In this way, the R-based Statistics Layer does not stand apart from downstream intelligence work. It helps prepare the analytical ground on which SOG can begin building clearer reporting, stronger recommendations, and more defensible client-facing intelligence products.
SOG Analysis is where Statistical Layer outputs evolve into the deliverables a client actually receives each month in their Client Intel Brief. At this point, analysts use those results to build intelligence products that explain external threat developments in practical terms, connect those developments to likely client exposures, and shape clear cybersecurity recommendations. This is also where the business rationale behind those recommendations is developed, so that proposed actions are tied directly to operational realities rather than offered in a vacuum.
For the client, this is where the value of External CTI-as-a-Service becomes real as a set of monthly deliverables. It is more than outside-the-firewall visibility, and more than a collection of interesting reports with no clear application. Our monthly intel briefs include elements such as attack scenario-based assessments, time-series forecasting of the external threat environment, dynamic attack progression impact mapping, business operations degradation modeling, technical cybersecurity recommendations, and the business operations justifications that explain why those technical recommendations matter in the client’s specific environment. In practical terms, External CTI-as-a-Service provides a clearer picture of external risk, along with intelligence and recommendations tied directly to the realities of the business.